Having trouble keeping up with your email? Catch up with Microsoft Copilot, your AI-powered assistant.


Having trouble keeping up with your email? Catch up with Microsoft Copilot, your AI-powered assistant.
Siloed identity and network tools leave gaps that attackers exploit, and employees experience through clunky sign-ins. The article, “Reimagine Secure Access With a Unified Approach,” shows how consolidating access management strengthens security, improves employee experience, and reduces cost. Read the article to see the benefits of unification, and contact A Systems Integrator to discuss how to take the next step.
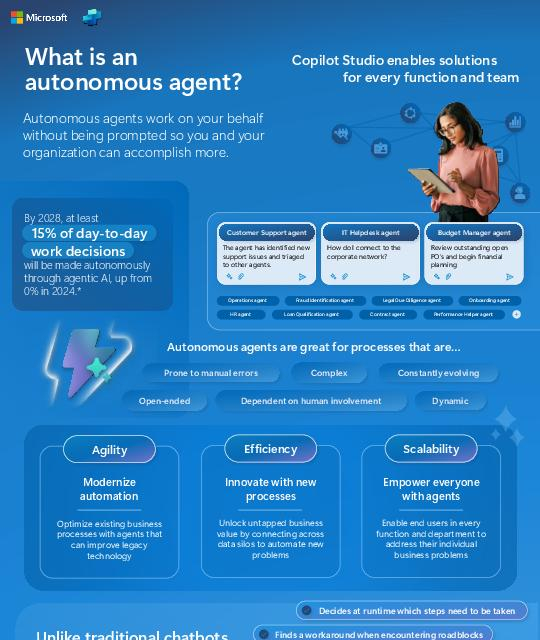
Manual processes slow productivity and increase the risk of error. This infographic illustrates how autonomous agents act on your behalf to streamline operations and solve problems proactively. View the infographic to understand how organizations are improving agility and efficiency with autonomous agents, and contact A Systems Integrator to explore how you can build your own.
As organizations expand their digital footprint, maintaining secure and seamless access across users, apps, and devices is a constant challenge. This customer story shows how Microsoft Entra Suite bridges identity and network access, enabling organizations to reduce complexity, strengthen protection, and empower users with frictionless experiences. Read the story to see how connected security delivers agility and confidence. Contact A Systems Integrator to discuss how unified identity and network solutions can strengthen your organization’s Zero Trust strategy.

Endless meeting coordination slows productivity. This infographic shows how AI-driven scheduling features help employees stay organized and focused. View the infographic to learn how CalMaestro helps teams reclaim control of their day and contact A Systems Integrator to start simplifying your scheduling today.
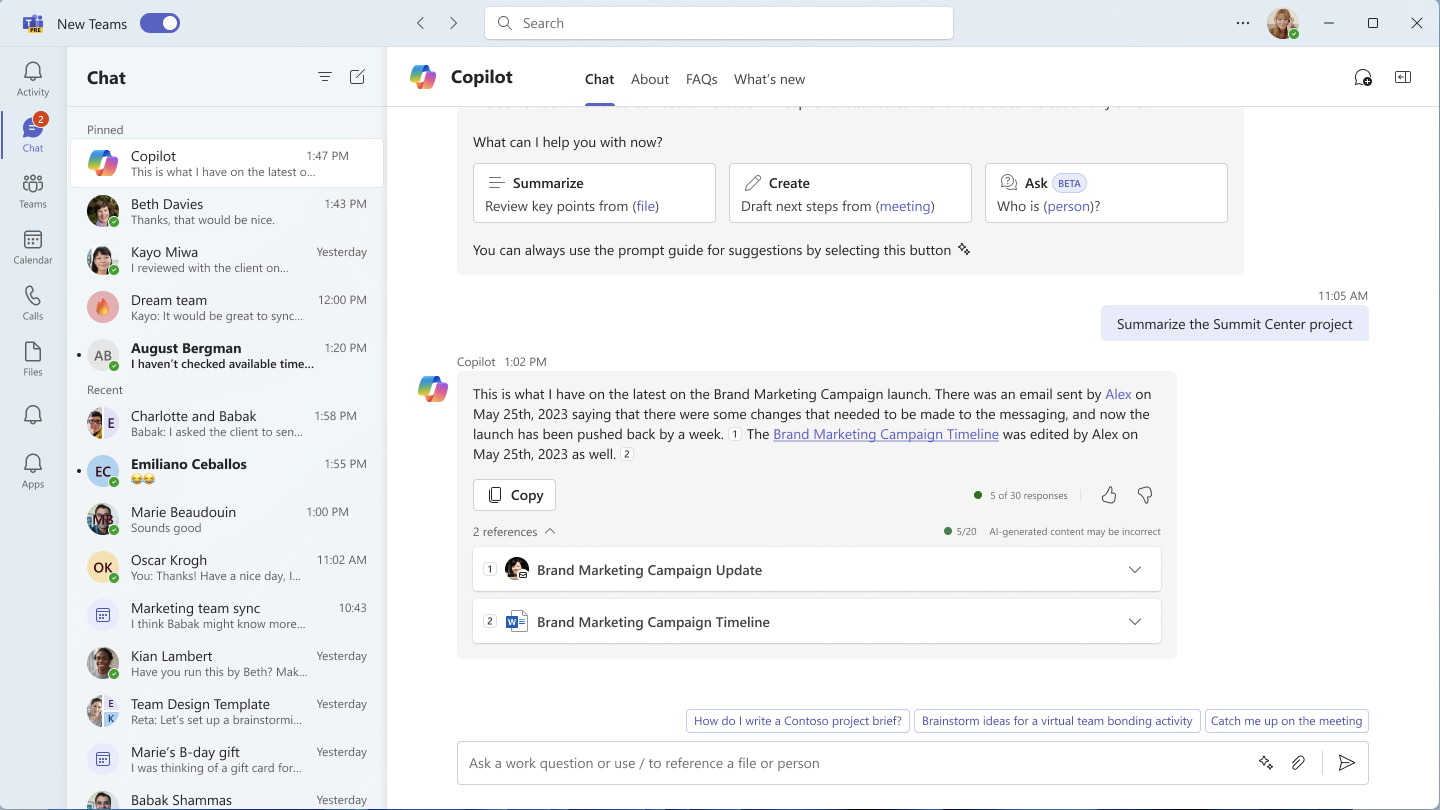
If you’re often spending time searching for the right chat message or trying to summarize a chat discussion, you’ll want to try out Microsoft Copilot in Chat.
Microsoft Copilot can help you be more productive by bringing together data from your documents, presentations and email in Microsoft Teams. Learn how in this Microsoft post.

Managing security across multiple identity and network tools increases complexity and risk. The eBook, “Secure Employee Access in the Age of AI,” reveals how unifying these access controls streamlines collaboration, reduces costs, and strengthens security posture. Download the eBook and connect with A Systems Integrator for guidance on creating a more cohesive security strategy.

Identity is the new perimeter, and attackers are exploiting it. The analyst report, “Identity-Centric Threats: The New Reality,” reveals how identity-driven attacks now account for nearly 60% of all confirmed incidents, powered by Phishing-as-a-Service platforms, infostealer malware, and credential marketplaces. Download the report for in-depth insights and contact A Systems Integrator for guidance on protecting your organization’s digital identity footprint.

Repetitive work slows productivity. Copilot Agents are changing that. This video highlights how Microsoft 365 Copilot Agents automate and execute business processes, supporting individuals and teams to work smarter. Watch the video for actionable insights, and contact A Systems Integrator for tailored advice on integrating Copilot Agents into your workplace.

Unproductive meetings cost companies countless hours each week. This infographic illustrates how AI-driven meeting summaries, automated task tracking, and translation features can reduce redundant meetings and accelerate decision-making. View the infographic to see how TeamsMaestro empowers teams to save time and collaborate more effectively. Contact A Systems Integrator to discuss how to deploy it in your organization.